The Application Gateway WAF v2 has brought some new features compared to v1, including the ability to create "WAF Custom Rules". In this short article I would like to discuss these "Custom Rules" and show how you can successfully create them. I have added some hints to the article that are difficult or impossible to find in the Microsoft documentation.
Feature overview WAF v1 vs v2
The function overview and the comparison of v1 with v2 of the Application Gateway WAF has been clearly presented by Microsoft under the following link. If you are interested in the other differences in addition to the "Custom Rules", you can find them there.
Microsoft Docs Feature Overview & Comparison
Application Gateway WAF v2 Custom Rules
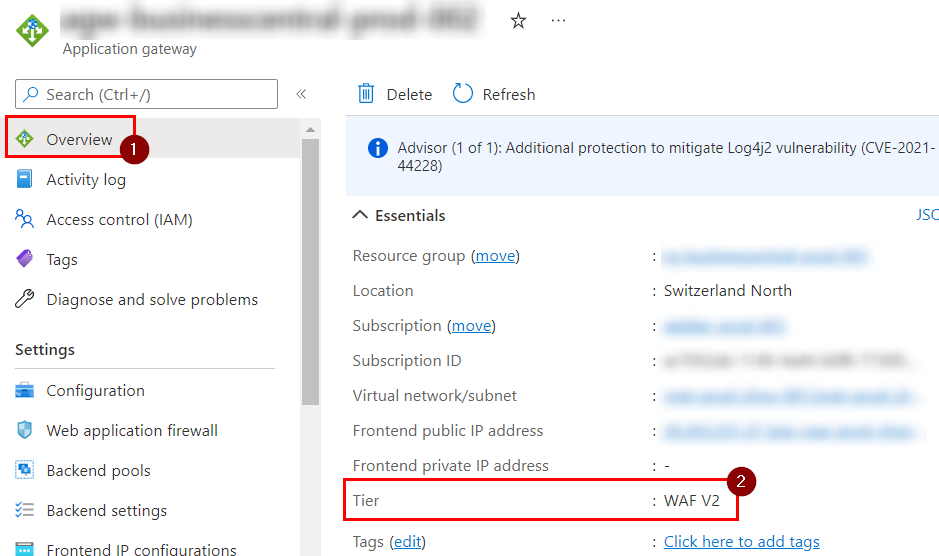
But now to the actual topic, which is the WAF Custom Rules of the Application Gateway. To create such custom rules, you can create an ordinary application gateway if it does not already exist. When you create it, you have to make sure that you select "WAF V2" for tiering.
Control the WAF version
If you already have an application gateway, but you do not know which version it is, you can easily check this in the portal or via PowerShell. In the portal, this can be seen directly in the overview.
With PowerShell the same is possible with the following command and results in the output as shown in the PrintScreen.
$appgw = Get-AzApplicationGateway -Name <AppGwName> -ResourceGroupName <ResourceGroupName>
$appgw.sku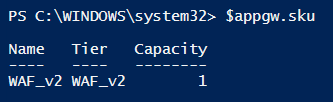
Creating the WAF v2 Custom Rules
Now that you have ensured you have the correct version of the Application Gateway, you can start creating the custom rules you want. Azure maps the WAF custom rules into a separate resource, which in turn is linked to the application gateway. To do this, proceed as follows.
- In the Application Gateway, under "Settings" and "Web application firewall", click on the name of the policy already associated.
- You will now be redirected to the "Application Gateway WAF policy" resource. There, navigate to "Custom rules" under "Settings", where you can now create a new custom rule.
- Klick on "Add custom rule"
Note:
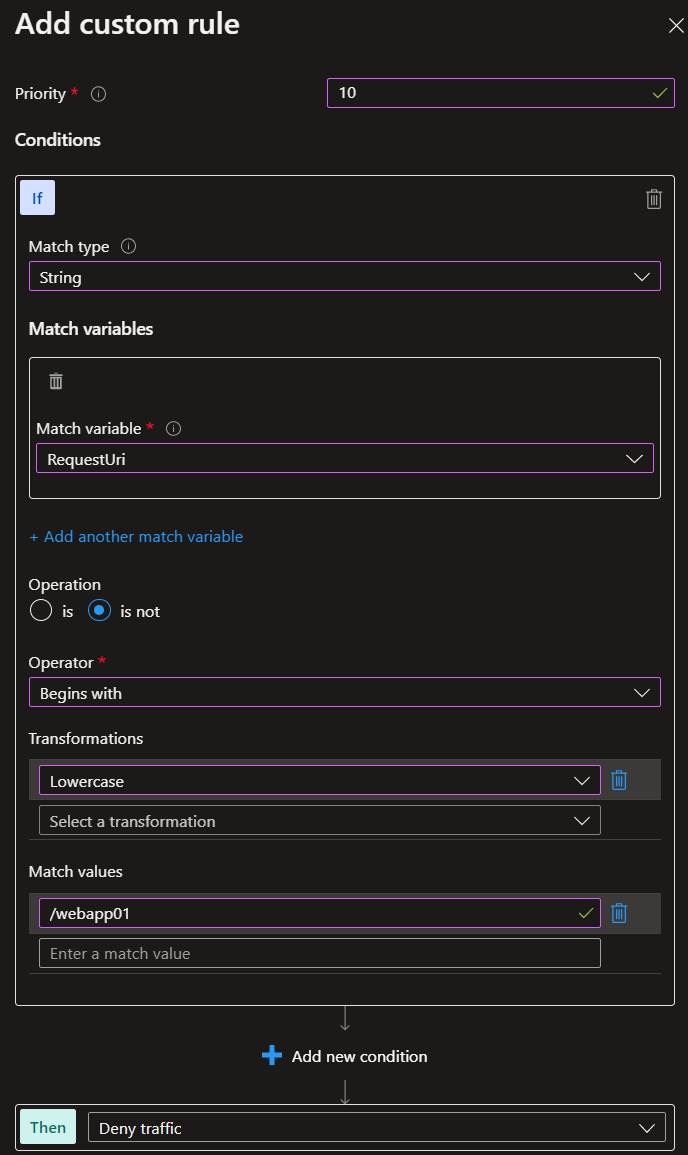
If you decide to work with the string "RequestUri" in the custom rules, note that only the path may be specified and not the full URI. So you shorten the full URI "https://graber.cloud/WebApp01" to just "/WebApp01".
The following is an example. In this custom rule, the URI is transformed to lowercase and then checked for the path "/webapp01". The operation is set to "is not" and the action at the bottom of "Then" is set to "Deny traffic". So any traffic that does NOT have this URI path is blocked. However, if the URI path is correct, the traffic is allowed and the standard rules of the application gateway also take effect.
Note on prioritization:
No matter how many custom rules you create, Azure will only apply a maximum of one. First, the custom rule with the lowest priority number is evaluated (i.e. priority 10 before 11 before 50...). If this rule applies, no more rules are evaluated and the action of the rule takes effect (e.g. "Deny traffic"). If the rule does not apply, the next one is evaluated in order of priority. However, if no rule applies, then traffic is basically allowed and the default rules take effect. "Custom rules are ALWAYS evaluated first, before the existing standard rules of the application gateway.
Detailliertere Informationen zum Regelevaluierungsprozess sind im Artikel Azure Application Gateway WAF Rules Evaluation zu finden.
With this guide and notes, you are now ready to create your own "Custom Rules" with the "Application Gateway WAF v2".
Sources:
https://docs.microsoft.com/en-us/azure/application-gateway/overview-v2?WT.mc_id=AZ-MVP-5004129

1 thought on “Application Gateway WAF v2 Custom Rules”