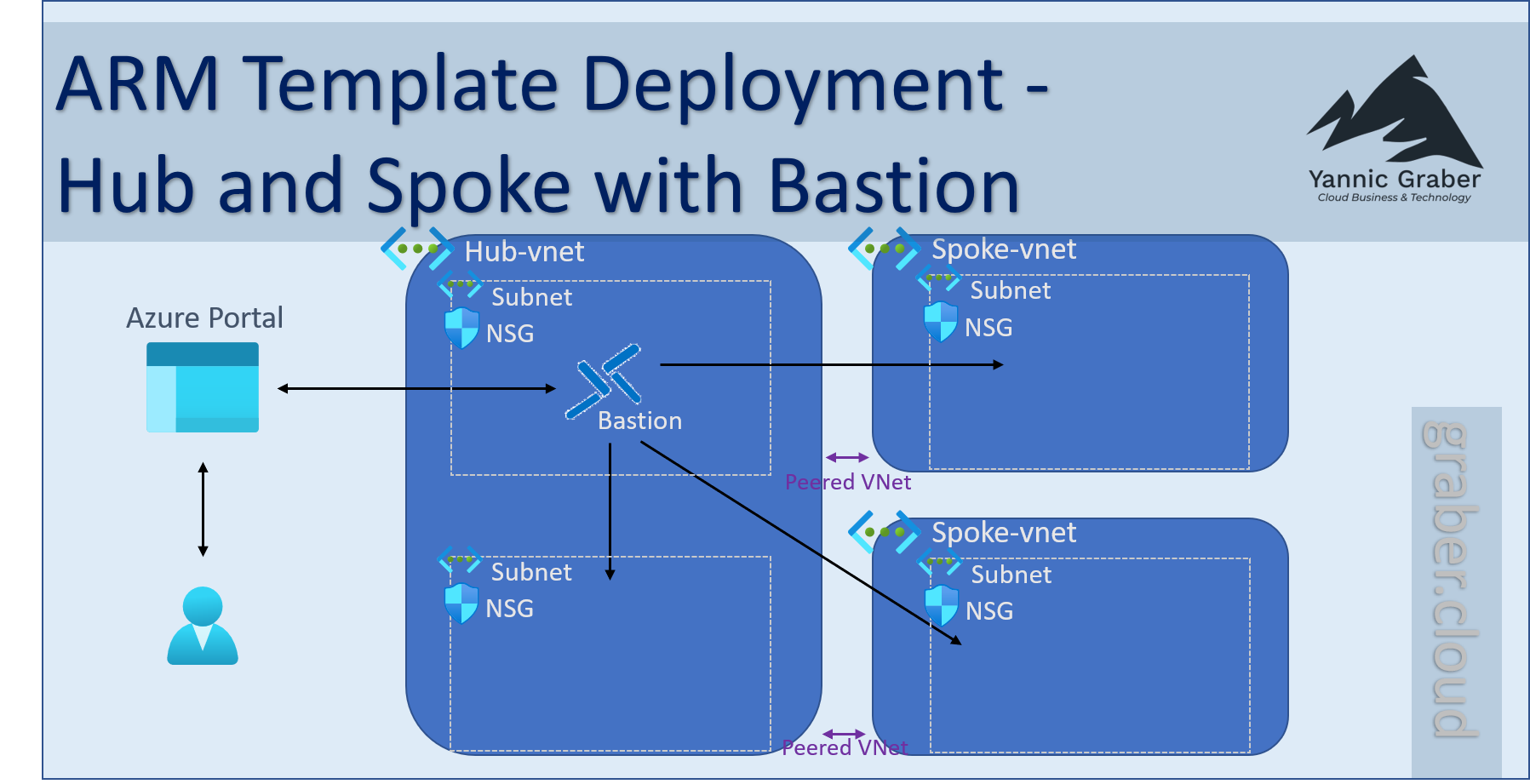
ARM template deployment – Hub and Spoke with Bastion
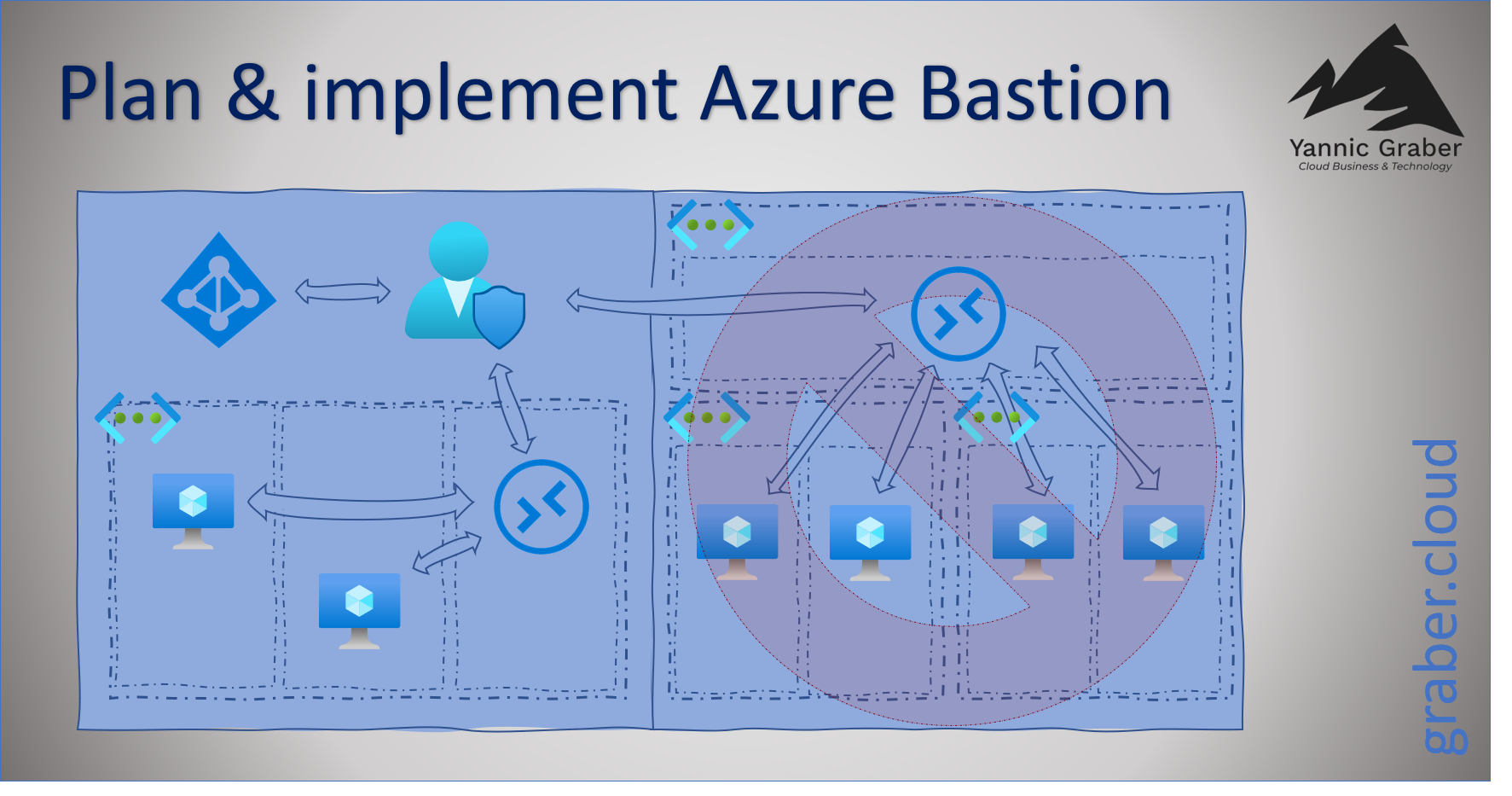
With an Azure Resource Manager (ARM) template, you can create a specific infrastructure on Azure with the click of a button. The template defines the infrastructure as code and Azure is thereby told the target state of the resources. I have created such a template and published it via Github. The ARM template deployment includes a hub and spoke network topology with a central Azure bastion for secure access to VMs. This post shows you step by step how to use the template for yourself.